What is a botnet?
We explore the phenomenon of zombie computer networks, explaining what are botnets used for and how they’re assembled
If your computer suddenly starts running very slowly, or behaving unexpectedly, there’s a possibility it’s been ensnared in a botnet.
If your first reaction to this is to ask “what are botnets?”, it’s important to understand how individual devices can end up being part of a hostile network of enslaved machines.
Because any web-enabled device can talk to any other web-enabled device, a malicious operator could try to install rogue program code on a machine anywhere across the internet.
Once this code is successfully installed and activated, it effectively hands control of the device to that operator, who might already have numerous other machines under their control.
The program code is often referred to as a bot. Bots are specialist software programs used to perform one repetitive, automated task to the exclusion of anything else.
That’s why a bot-infected device will run very slowly, because all its available resources are being redirected to one task.
We’re using the word ‘device’ rather than ‘computer’ because botnets can harness most web-enabled devices – webcams, routers, Android smartphones, even smart kitchen appliances.
What are botnets used to do?
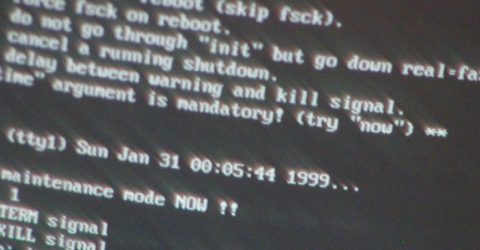
An attacker will create or modify malware which is then delivered to an unsuspecting device, before being installed and activated.
(We’ve previously discussed how to avoid malware, including the Trojans where malicious code is hidden inside a seemingly legitimate file or web link.)
Once they’ve enslaved enough remote devices, a botnet operator will instruct their network of zombie devices to begin work on a mass activity:
The advantages of using a botnet include the sheer wealth of resources which can be brought to bear.
Few servers can cope with tens of millions of individual connection requests being made each and every second, lasting days at a time or even weeks on end.
It’s also very difficult to find the originator of a botnet, since every machine in the network has the same status, collectively cloaking the presence of its operator.
Where do botnets come from?
While it’s become fashionable to blame Russia for all the world’s woes, on this occasion, they really do have to accept a large degree of responsibility.
Data from the end of last year by globally-respected (and politically neutral) anti-spam organisation Spamhaus revealed Russia leads the world in botnet attacks.
Russia is hugely ramping up its botnet activities as the war in Ukraine grinds on, contributing to a 12 per cent rise in global botnet activity over the first quarter of 2022.
The targets may be individual ISPs, companies or entire governments. Victims this year have included the Ukrainian postal service, Italian publishers and the German Bundestag website.
Motives range from state-sponsored attacks on other nations through to sheer devilment – though financial gain is inevitably a key motivator for many criminal gangs.
After all, botnets aren’t easy to assemble. The Command and Control software required to run them is complex, and modern-day adaptive DDoS attacks take a lot of planning.
That said, botnets like Mirai and Emotet continue to plague the world several years after they were first developed, suggesting that older bots remain highly effective here in 2022.
Even a slight tweak to established botnet software reinvents it as an unrecognised threat among antivirus packages and firewalls.
Known as a zero day attack, this is perhaps the most dangerous form of botnet – one which even antivirus software that’s updated daily might not have registered yet.






