How do remote computer connections work?
We’ve traditionally viewed desktop computers as standalone machines, but the advent of cloud computing has changed everything.
Today, we stream movies and music online, use computers for socialising and communicating, and even access programs and documents via the cloud.
Even so, remote computer connections still seem strangely exotic.
This is the process of accessing a desktop or laptop from another device, via the internet.
NewsGoogle staff will work from home until at least July 2021
An external keyboard and mouse are used in lieu of the device’s own peripherals, with full access to every function, file and folder.
Help is on the way
The primary deployment of remote computer connections revolves around offsite IT support.
Tech firms around the world now provide cost-effective ad-hoc support for technical issues.
Providing your computer is still connected to the internet, an IT officer in any location could take control of it and attempt to tackle any gremlins.
For the end user, there’s something surreal about watching the mouse cursor whizz around the screen by itself.
It’s a bit like watching a mechanic drive off in your car – officially sanctioned, yet strangely unsettling.
Fortunately, robust security protocols are in place, to prevent remote desktop software being used without authorisation.
Making a connection
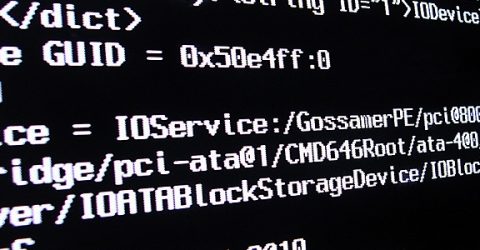
The computer being accessed is referred to as the host, while the device controlling it is known as the client.
Both machines need the same piece of software to be installed, such as Windows Remote Desktop, Splashtop SOS or Remote Utilities.
Although a client accessing Chrome Remote Desktop might be running any type of machine, they’ll need the Chrome browser installed to access a Chromebook remotely.
To initiate a remote access session, a code or key will be given to the client by the host.
In the case of Splashtop SOS, the host device generates a unique nine-digit security code, which might be relayed to the client operator over the phone or via an email/text message.
When the operator enters this into their own machine, a secure connection is established between both devices.
The client immediately has full control over the host machine, using their own peripherals to navigate around.
They can do anything the host could, such as opening programs or adjusting settings.
Self-service
Remote computer connections ensure affordable IT support is available whenever and wherever you need it.
It’s ideal for the self-employed and anyone based in an isolated location.
Potential uses extend beyond IT troubleshooting, as well.
If you’re not a fan of cloud-hosted documents, remote computer connections provide a way to access files from your C drive while you’re out and about, or working from home.
MoreWorking from home boosts Britain’s productivity
You could help a less tech-savvy relative install a peripheral device or run an antivirus scan from hundreds of miles away.
Colleagues or associates may be granted access to certain portions of your computer (such as calendars and spreadsheets) to eliminate data siloes.
And anyone unexpectedly out of the office (due to ill health, bad weather or a domestic emergency) could still turn in a full day’s work.






