Don’t Click: Fake Herbalife email ransomware sweeping globe
Email ransomware thought to originate in Greece or Vietnam is spreading rapidly across multiple countries, according to security researchers at US-based Barracuda Networks.
The threat started circulating sometime on Tuesday 19 September with millions of attacks developing hour by hour.
“We are actively monitoring an aggressive ransomware…so far we have seen roughly 20 million of these attacks in the last 24 hours, and that number is growing rapidly,” said lead platform architect Eugene Weiss at Barracuda’s Advanced Technology Group.
What to watch for
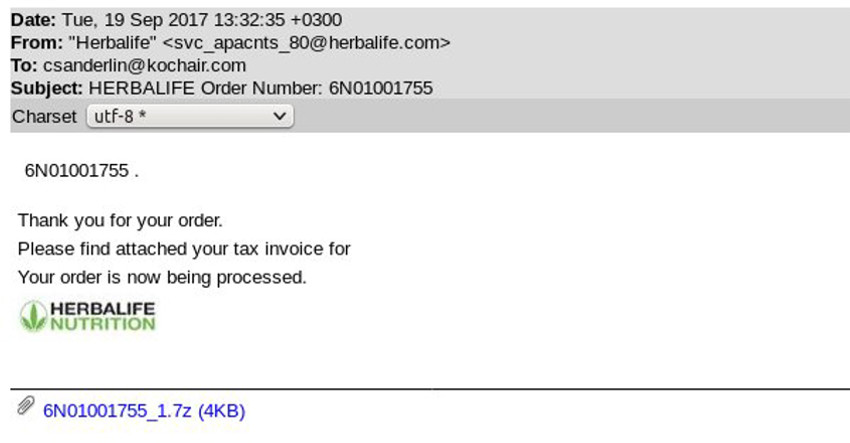
It begins with a fairly standard and unsophisticated spamming technique.
- First a faked email purporting to be from nutrition supplement company Herbalife drops into a users’ inbox.
- Then, it locks up the computer of anyone who clicks on a link which states “payment is attached”.
Don’t click and whatever you do, don’t pay
The cybercriminals behind the attack could not restore your work even if they wanted to, says Weiss.
Even if you pay the ransom to get your computer unlocked, you won’t get your work or your files back.
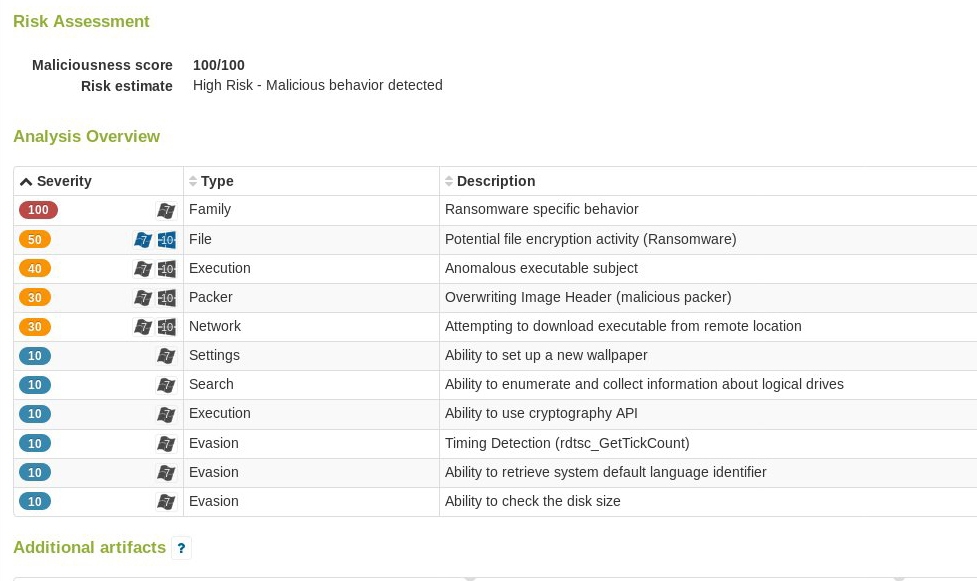
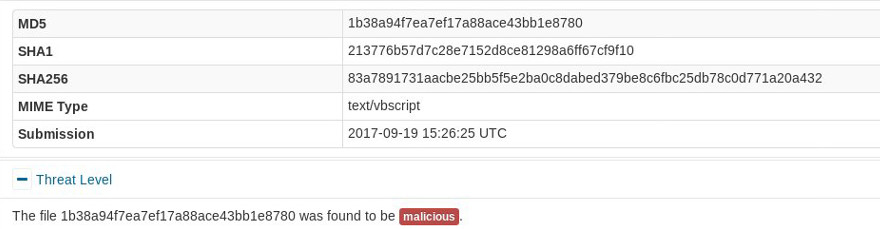
Barracuda researchers have confirmed that this attack is using a Locky variant with a single identifier.
The identifier allows the attacker to identify the victim so that when the victim pays the ransom, the attacker can send that victim the decryptor.
In this attack, all victims get the same identifier, which means that victims who pay the ransom will not get a decryptor because it will be impossible for the criminal to identify them.
It might sound obvious that you shouldn’t hit a link in an email you don’t recognise.
But this attack works because, as Weiss told Axios, it bypasses any technical hack and instead uses the psychological tactic to get someone to click on something they know they shouldn’t.
These attacks are being automatically generated but with a template that randomizes parts of the email.
So the domains used to send them out are constantly changing and bypass standard security offered by anti-virus engines.
Stay safe: Have I been pwned? Spambot harvests 711 million email addresses
From NHS to you
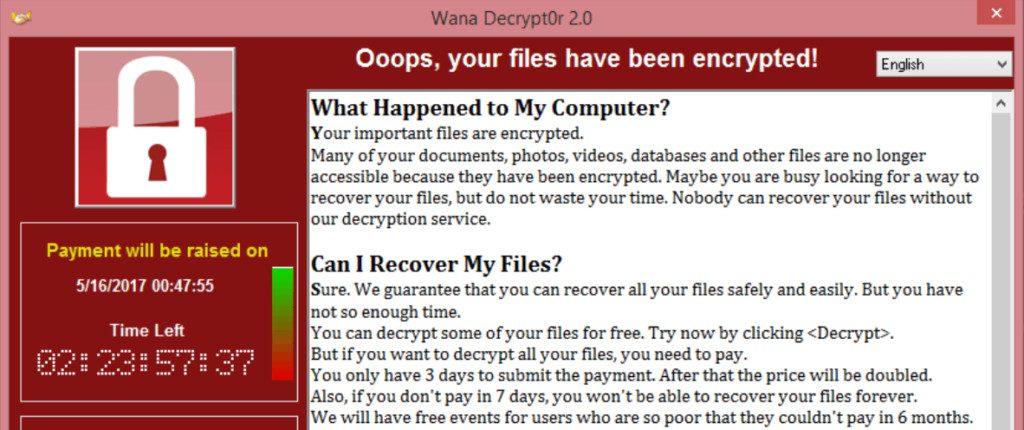
Ransomware hit the headlines in May when a malware variant of the Wanna Decryptor, dubbed WannaCry, brought down NHS computer systems at 16 UK hospitals.
Nurses were shocked to see their screens freezen when they tried to access patient records, followed by a pop-up demanding cash ransoms of between $300 and $600 in Bitcoin.
Accident and Emergency departments up and down the country for forced to divert ambulances as staff were urged to turn off their machines. The attack stoked fears that criminals could relatively easily exploit known weaknesses in crucial IT systems.
WannaCry malware has been detected 36,000 times in the past year and it has already infected targets in 11 countries.
What to do
Delete, ignore, move on
If your email spam filter doesn’t block the ransomware email, just delete it and move on.
Tell your friends
Everyone appreciates a heads-up warning and while UK reports have been limited so far this could easily find its way on to a laptop near you.
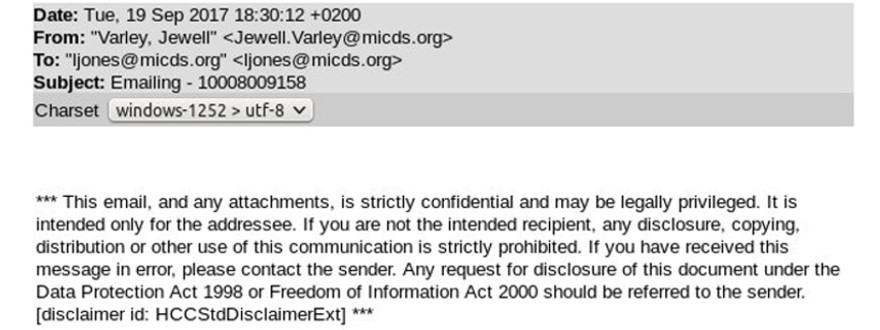
Update: A new variant of the ransomware appeared on Tuesday evening, Barracuda say.
It will appear with the subject line “Emailing – (attachment name)” as in the picture below.