Revealed: how hackers use compromised passwords
Compromised passwords are a popular target for hackers and scammers – and many of us are in the firing line.
In the darker corners of the internet, criminal activities like hacking and data theft are often treated as services which can be outsourced and delegated.
If you want to defraud vulnerable people, you don’t necessarily have to do it yourself. Third parties and automated tools could do much of the legwork on your behalf.
Many years ago, a combined database of information gleaned from multiple website data breaches was shared online, in a groundbreaking move by hackers.
Known as a combolist, it blended passwords from numerous websites, allowing anyone in possession of it to cross-reference passwords and email accounts for multiple matches.
It also gave them ammunition to conduct a far more insidious process, which has now become one of the leading forms of data theft and user accounts being compromised.
Combolists are key to a process known as credential stuffing, where acquired passwords and email addresses or usernames are entered into numerous unrelated websites, in the hope they provide a successful login.
Combolists and credential stuffing perfectly illustrate how stolen user data circulates across the internet long after it’s been acquired – and why password safety is so vital.
Automatic for the people
The automated tools which mindlessly pump email addresses and compromised passwords into random website login pages have a specific purpose.
They rely on people using the same login credentials across multiple online accounts, enabling a bot conducting brute-force data entry to find a way into other customer accounts.
Once logged into another account, hackers can wreak havoc – ordering goods and services, harvesting payment data, locking the user out of their own account, and so on.
A customer could end up being defrauded from several accounts sharing the same password, while being unable to access those accounts after the scammers reset login credentials.
A password compromised several years ago could be the culprit in a theft happening tomorrow, if it’s still being used to guard other online accounts.
What’s being done about compromised passwords?
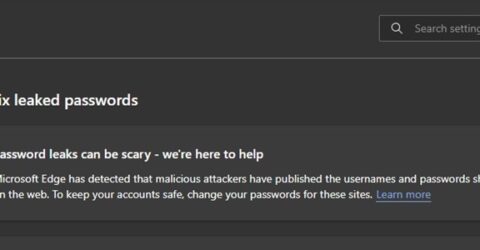
Web browsers are increasingly attuned to the risk of passwords being maliciously acquired.
As an example, Edge will notify users if a recently entered password has been recorded on historic lists of hacked password credentials, encouraging users to reset their details.
Many antivirus packages conduct similar checks, raising “this password has appeared in a data leak” messages if they detect a current password in a historic leak.
However, human error remains the biggest threat to password safety.
Common mistakes include reusing the same password (or numerical variations) across multiple accounts, leaving accounts logged in and accessing them via public WiFi networks.
What should I do to stay safe?
It’s easy to say (and harder to do), but the best defence against credential stuffing bots is to use a different password for every online account.
You don’t need an eidetic memory. Write passwords down in an offline location (such as a notebook in your desk drawer) or add abbreviated reminders into your web browser Favourites list.
An alternative is to use a password manager, which we’ve previously reviewed. They generate and store unique passcodes for each account, with a single master password to remember.
Two-factor authentication is a damned nuisance at times, but it thwarts any credential stuffing bots.
Never access secure or financial websites over insecure public WiFi connections – avoid ecommerce transactions in coffee shops, or logging into online banking in a shopping centre.
Use a VPN to cloak data transfers, or install the Tor browser if your home internet connection is fast enough to counteract Tor’s sluggish data transfers.